A Security Group works as a firewall, allowing you to define both “allow” and “deny” rules. A source can be an internet address or a security group, and a security group can be assigned to a Virtual Machine or a subnet.
Refer to the Azure documentation for more information.
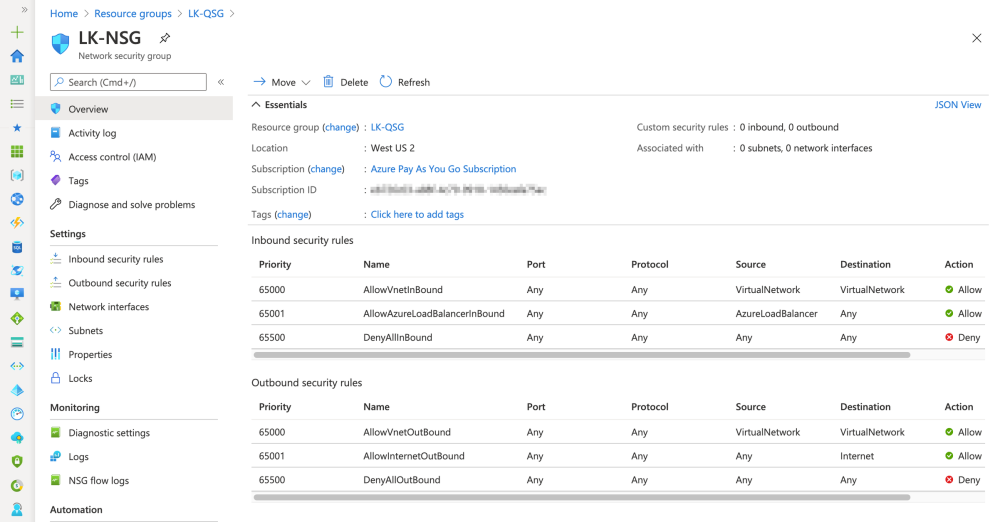
A new security group already has several “allow” and “deny” rules (those are defined with priority 65xxx). We will add following additional rules to “allow” access (see the green arrows).
- Allow traffic from the work location to LK-subnet
- Allow traffic from Virtual Machines to Internal Load Balancer

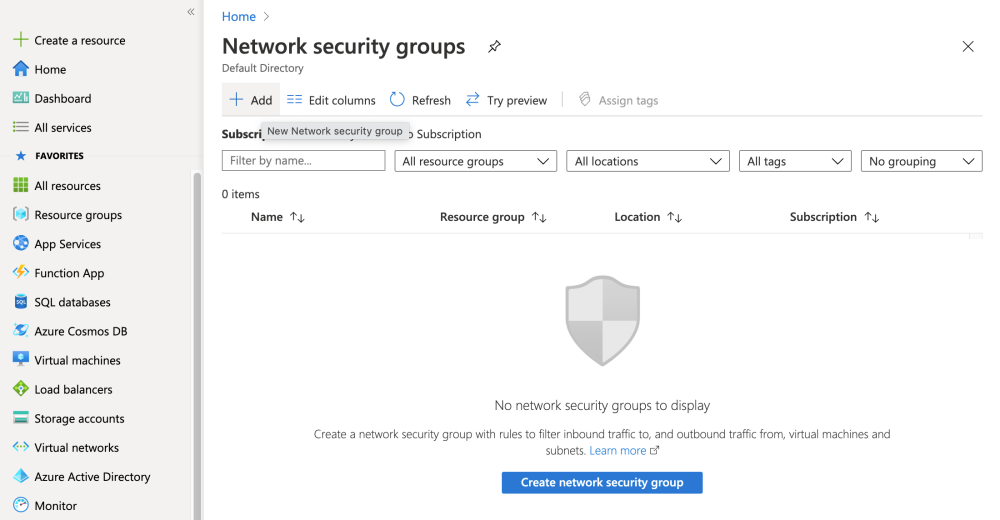
- Select “Network Security Group” from the home screen and click “Add” to create a new one.
- Select the Resource Group LK-QSG, specify the name of new security group as LK-NSG, then select a region.
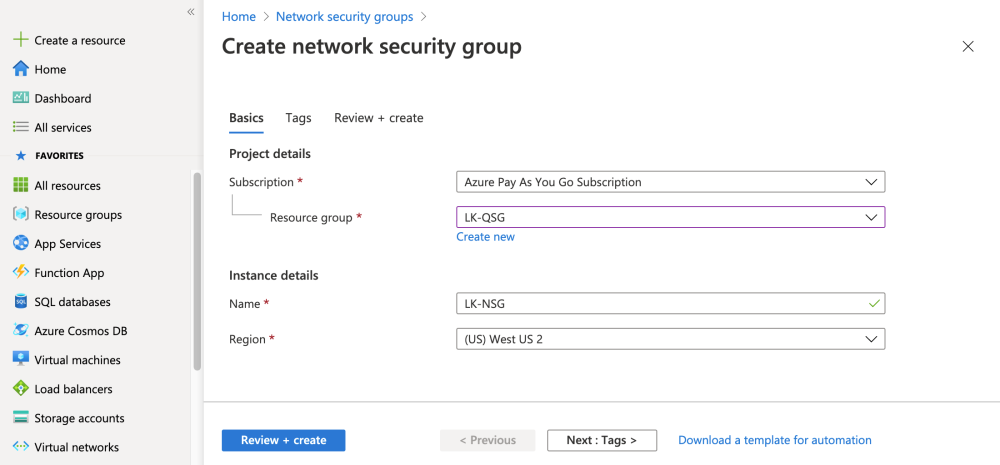
Once you specify the values, click “Review + create”.
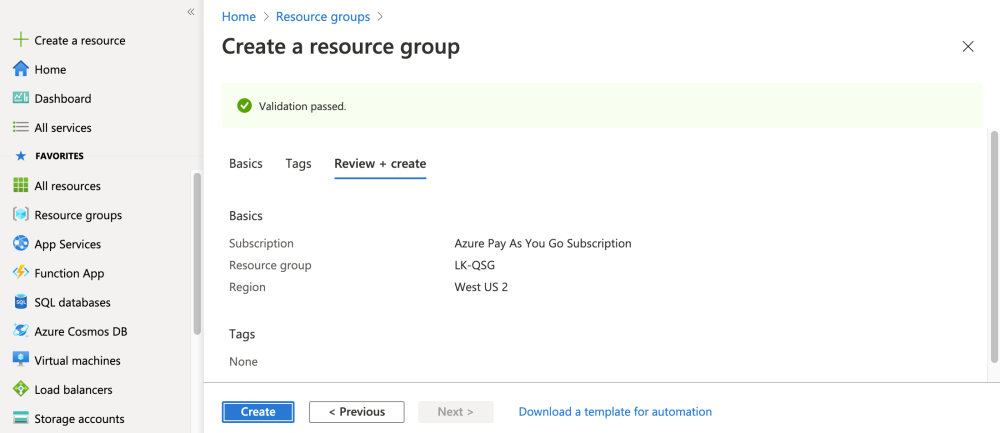
- Once the wizard validates your input, click “Create”.
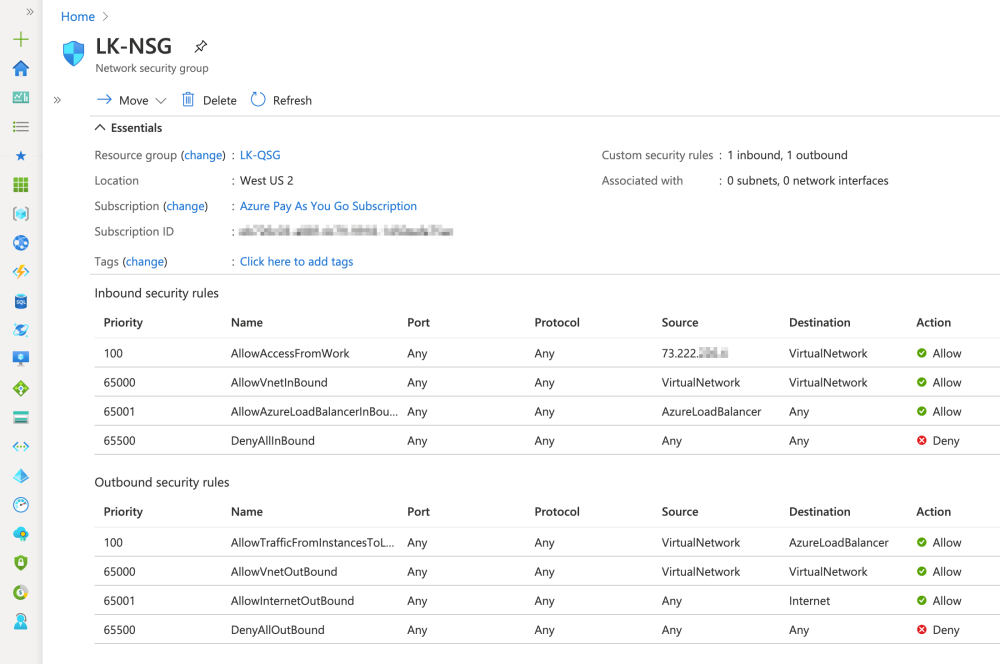
- The new security group LK-NSG is now created. You can see that there are several inbound and outbound rules already defined.
- Select the Inbound security rules from the left side and click “Add” to enter the new rule. Enter the following values:
- Source IP: Your WAN IP address(es)
- Source Port Range: *
- Destination: Virtual Network
- Destination Port Ranges: *
- Name: AllowAccessFromWork (any name that represents this configuration is fine)
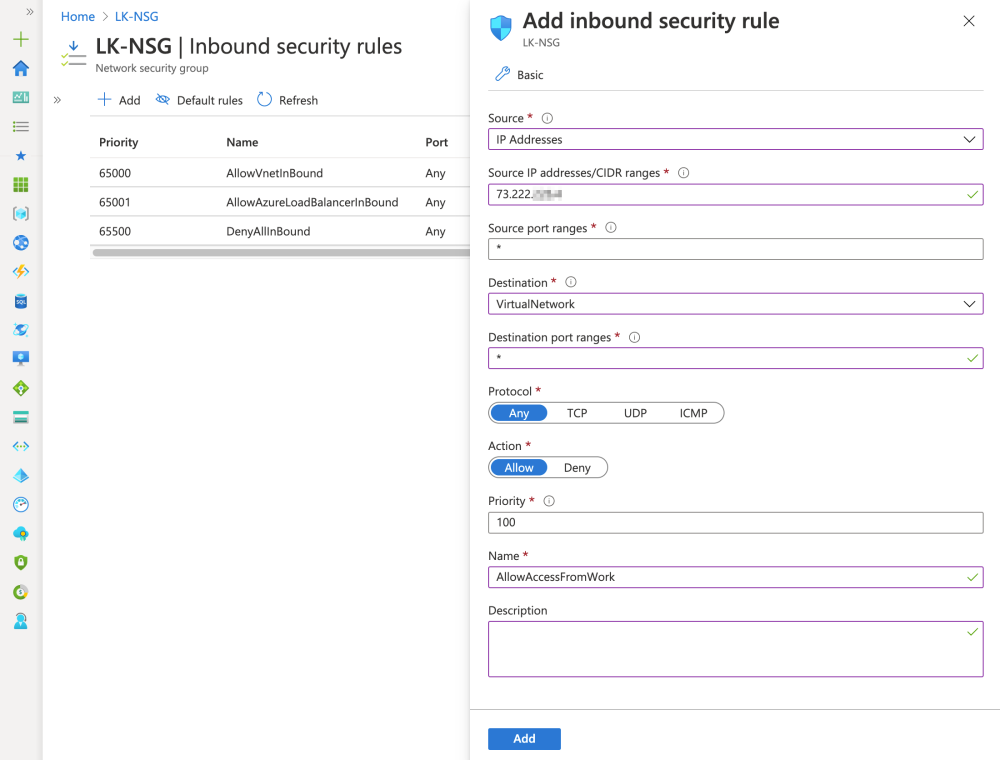
After you enter the values, click “Add”.
- Select Outbound security rules from the left side and click “Add” to enter the new rule. Enter the following values:
- Source: VirtualNetwork
- Source port range: *
- Destination: Service Tag
- Destination Service Tag: AzureLoadBalancer
- Destination port ranges: *
- Name: AllowTrafficFromInstancesToLoadBalancer (any name that represents this configuration is fine)
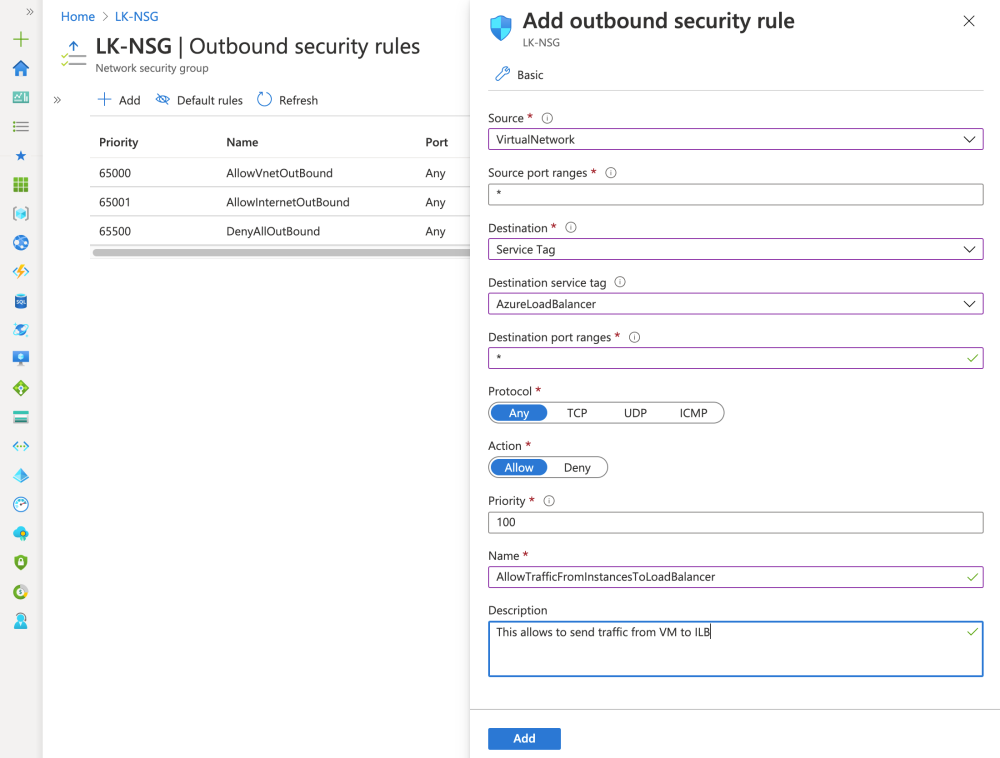
After you enter the values, click “Add”.
- Now the new Security group is defined.


Post your comment on this topic.