A Typical Resource Protection Scenario with LifeKeeper
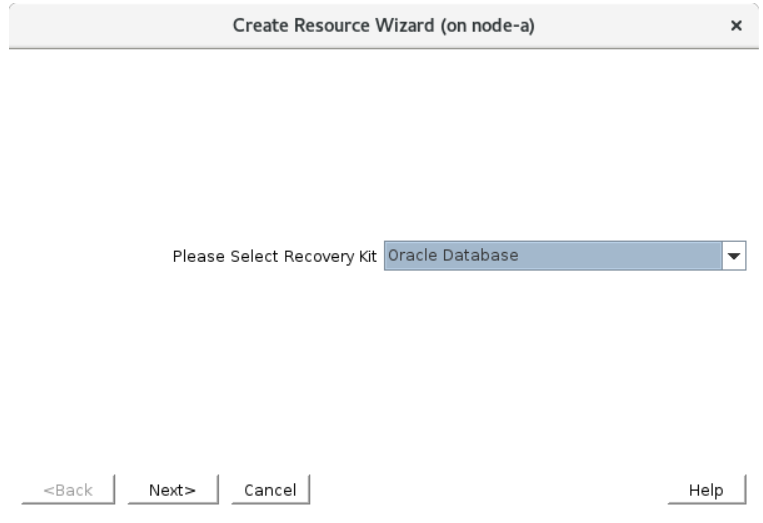
With LifeKeeper, most of the configuration can be completed using wizards. The wizard collects information about the resource(s) that are available for protection, and these resources can be protected by answering a series of simple questions. In most cases it is only necessary to select the default parameters. A standard example of LifeKeeper resource creation is given below.
- Create Resource Wizard
a. Select Resource Type (IP Resource, Data Replication, Oracle, etc.)
b. Select Switchback Type
c. Select the “active” server (where the application is currently running)
d. Select the IP address to protect, configuration file location, and disk to protect
e. Select the Resource Tag (name)
f. Review the selections
- Pre-Extend Wizard
a. Select the target server (which will take over as the application host in the event of switchover or failover)
b. Select Switchback Type
c. Select the Priority
d. Review the selections
- Extend the Resource Hierarchy
a. Select the IP address of the target, configuration file location, and disk to replicate data to
b. Select the Resource Tag (name)
c. Review the selections
- Hierarchy Integrity Verification
Once the configuration is completed, the wizard also automatically defines the dependencies between resources (for example, to protect a database resource it is necessary to mount the underlying disk(s) before starting the database).
Switching Between Nodes
We are now ready to protect our resources.
As discussed earlier, cloud environments work differently than on-premise environments. If you are using a cloud environment, please read through Switching between Nodes in a Cloud Environment for relevant information about routing traffic to the active node in a cloud environment. We will configure the necessary resources after creating the IP resource, and the parameters selected for the IP resource in the next section will vary based on the cloud environment used.
If working in an on-premise environment, simply going through the following page is sufficient.
If working in a cloud environment, select the relevant scenario from the following page:
Once the IP resource is protected, it is recommended that you initiate a switchover (where the “standby” node becomes the “active” node) to test the functionality.
Setup Disk Replication
In most scenarios, data replication should be defined between nodes (especially when evaluating in the cloud). Follow the steps below to define data replication between nodes.
Protect our Resources
Once the basic preparation is completed, you can now protect resources such as databases and applications.


Post your comment on this topic.