A Security Group works as a firewall, and “allow” rules can be defined from each source. A source can be an internet address or security group, and a security group can be assigned to an Elastic Network Interface. As a network interface is attached to an Instance, this works as a firewall rule for each instance.
Refer to the AWS documentation for more information.
In this section, we will define two “allow” rules as follows:
- Allow access from the remote work location.
- Allow access between instances (node-a and node-b). This is done by allowing the same security group as the source and then assigning the same security group to both instances.
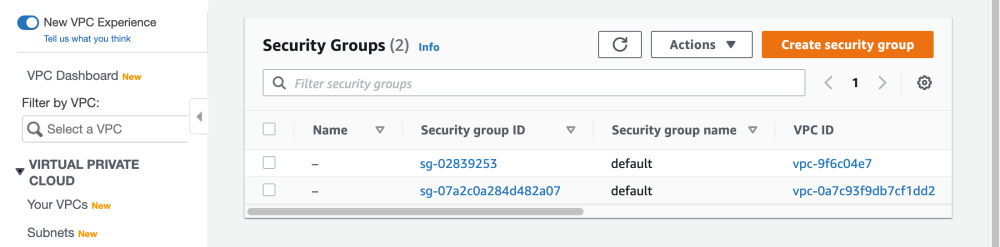
- Select “Security Groups” from the left navigation pane. As previously mentioned, default security groups will already exist. Click “Create security group”.
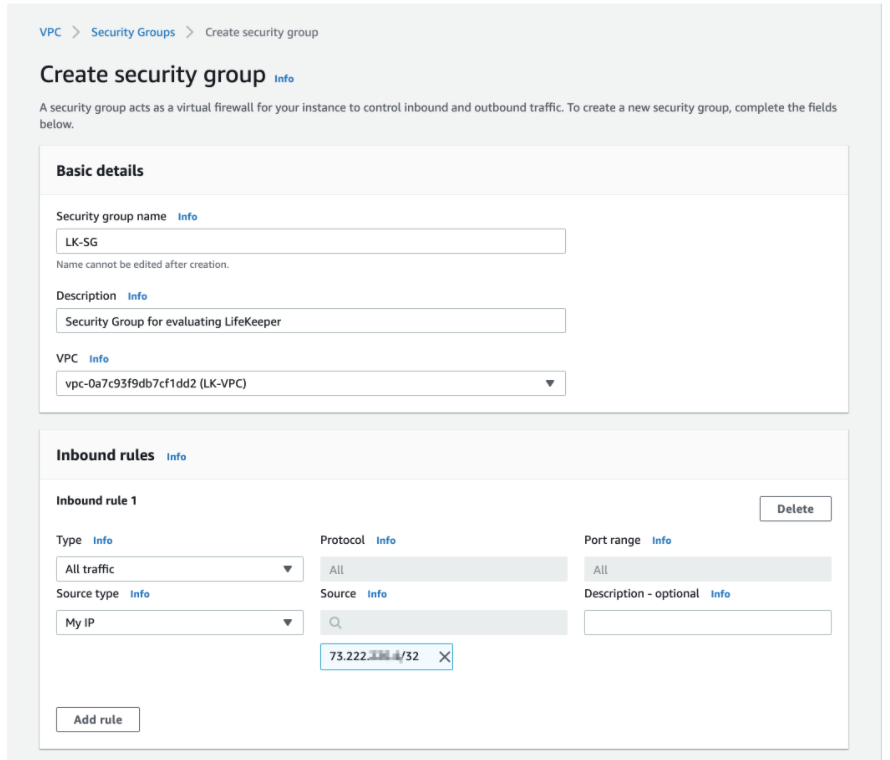
- Enter the values for the new security group as shown in the screenshot using the following parameters:
- Name: LK-SG
- VPC: LK-VPC
- Create the first Inbound Rule. Select “Add Rule” and select “All Traffic” as the type (for now). Then select “My IP” as Source type. This automatically selects the user’s WAN address as source. If required, update the source address range based on the in use WAN address (it may be appropriate to change this from a specific IP address to a range of IP addresses).
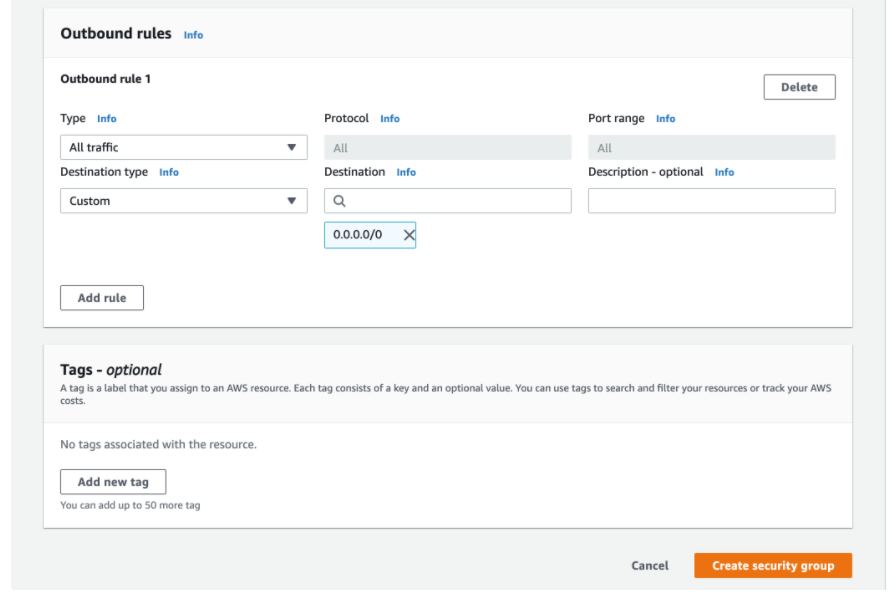
Once the values are confirmed, click “Create security group” at the bottom right.
- Once new security group has been created, click “Edit inbound rules” to allow traffic within the same Security Group.
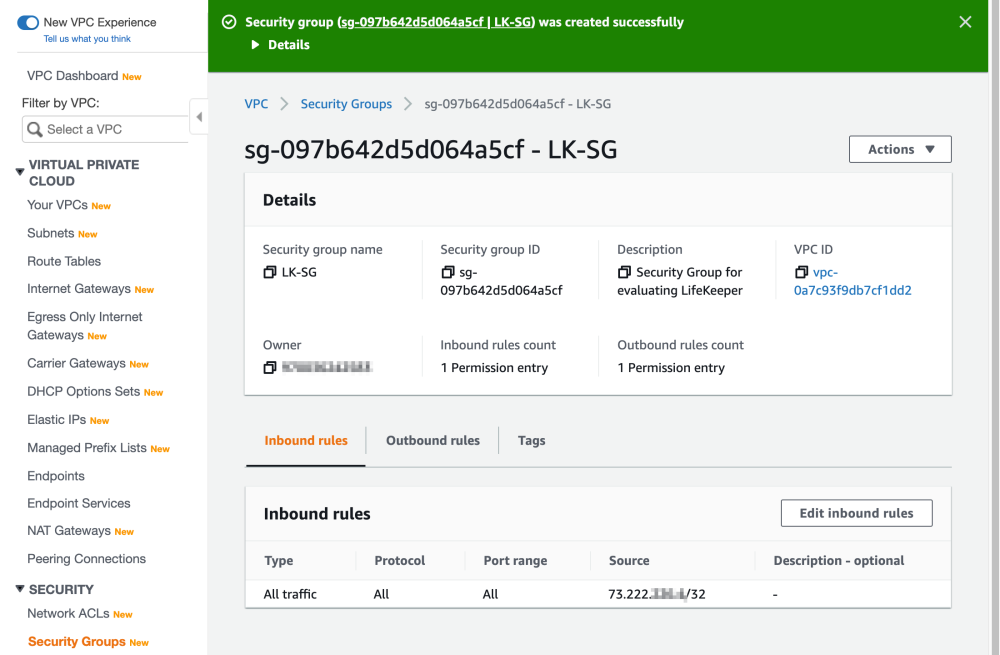
- Once the “Edit inbound rules” page appears, select “Add rule”, then select “LK-SG” (which we just created). With this change, any instances that are associated with “LK-SG” can communicate with each other.
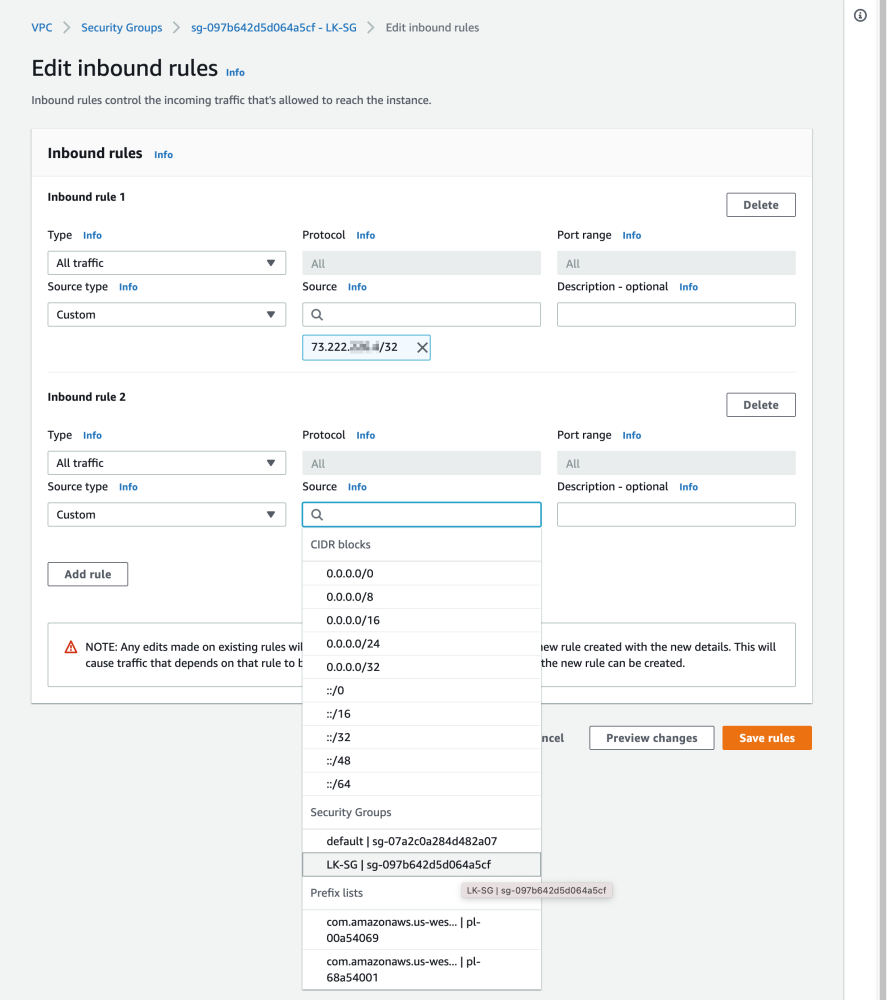
Once the change is confirmed, click “Save rules”. The Security Group is now created.
- Confirm the parameters for the newly created Security Group.



Post your comment on this topic.