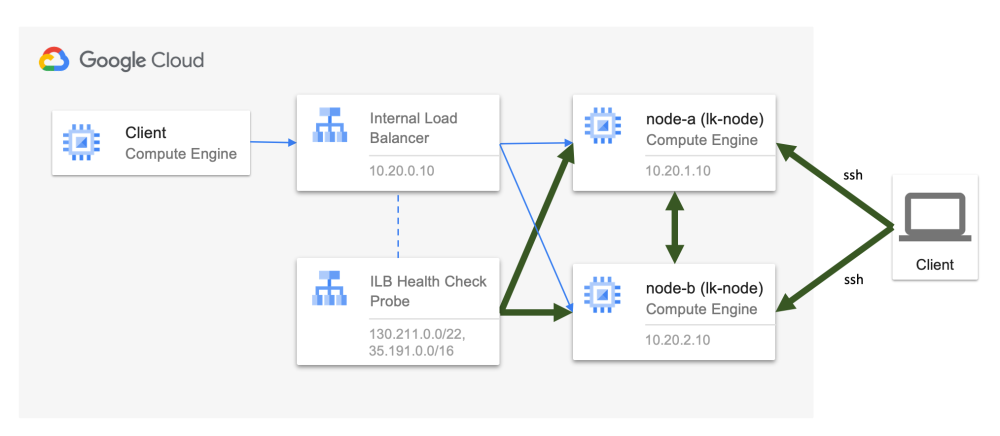
With a set of firewall rules, you can define both “allow” and “deny” rules for each type of traffic. A source can be an internet address, an Internal Load Balancer, or a group of VMs. A group of VMs is identified by a tag assigned to a VM.
Refer to the Google Cloud documentation for more information.
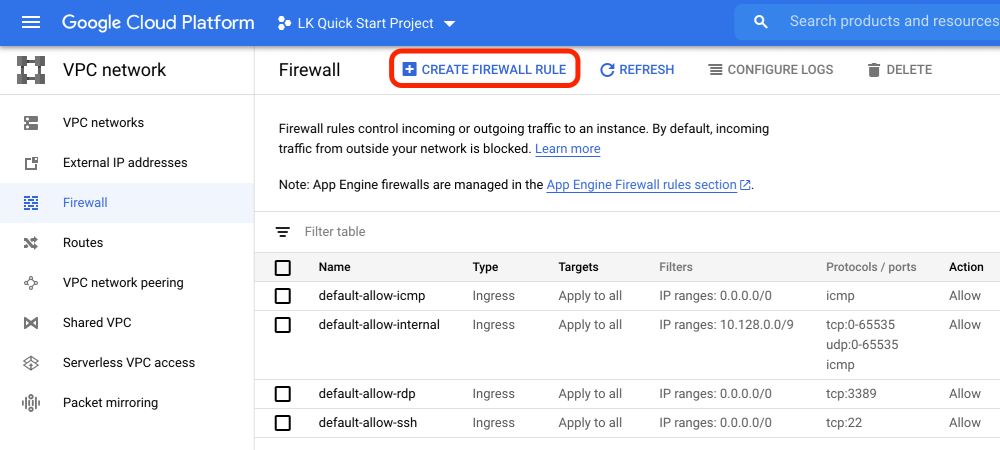
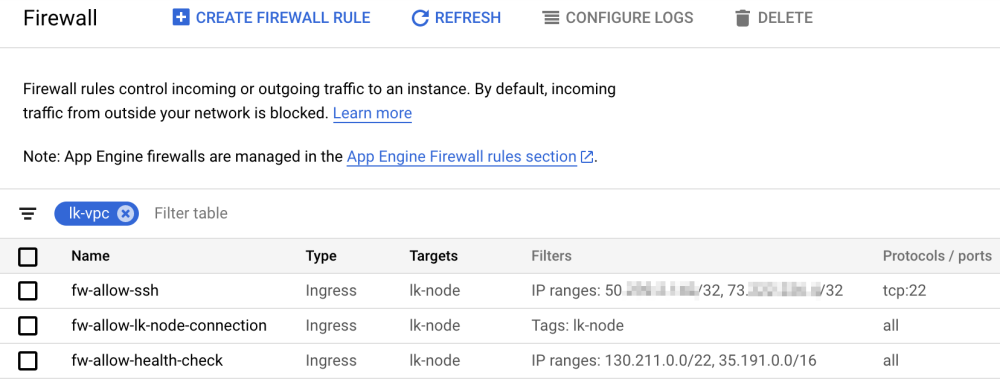
Once you go to “VPC network” > “Firewall”, a set of firewall rules are already defined for the “default” VPC. Now we are going to define the following rules for lk-vpc.
- Allow ssh traffic from your remote work location to VMs with lk-node tag. (fw-allow-ssh)
- Allow all traffic between VMs with lk-node tag. (fw-allow-lk-node-connection)
- Allow all health check probes from the Internal Load Balancer to VMs with lk-node tag. (fw-allow-health-check)
The traffic allowed by these firewall rules is highlighted by the thick arrows in the diagram below.
The following table outlines how we should configure these rules.
 Common values across VM Common values across VM |
Network | lk-vpc |
|---|---|---|
| Type | Ingress | |
| Target | lk-node | |
| Action | Allow | |
| fw-allow-ssh | Priority | 1000 |
| Source | WAN IP Address of work location | |
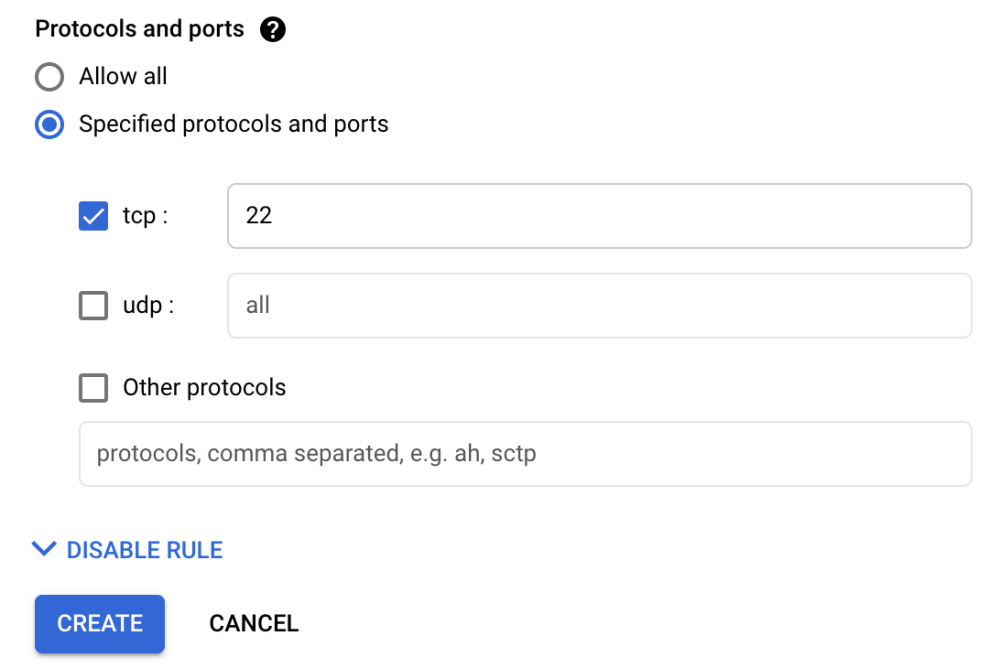
| Protocols / ports | tcp:22 | |
| fw-allow-lk-node-connection | Priority | 1100 |
| Source | Tags: lk-node | |
| Protocols / ports | all | |
| fw-allow-health-check (*1) | Priority | 1200 |
| Source | 130.211.0.0/22, 35.191.0.0/16 | |
| Protocols / ports | all |
(*1) Google Cloud Documentation on Load Balancer Health Check Probe
- Select “VPC network” > “Firewall” from the home screen. Now you see a list of firewall rules for the default vpc. Click “CREATE FIREWALL RULE” located at the top and create the first rule “fw-allow-ssh“.
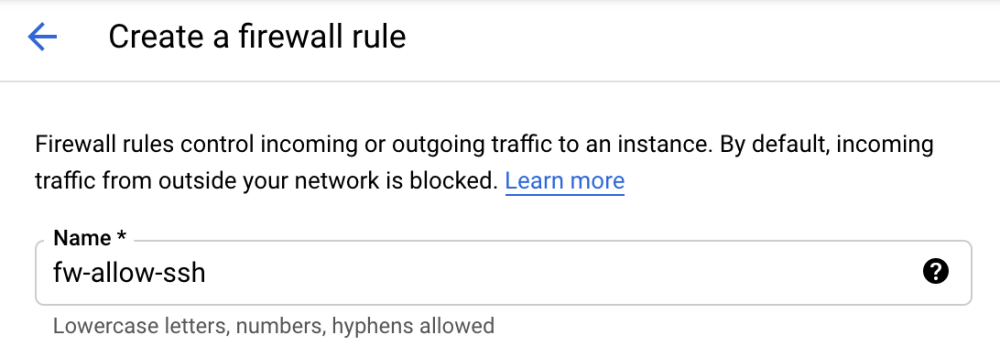
- The following steps describe how to allow an ssh connection from your work location so that you will be able to configure the node from your work location. In the “Create a firewall rule” wizard, specify the name as fw-allow-ssh.
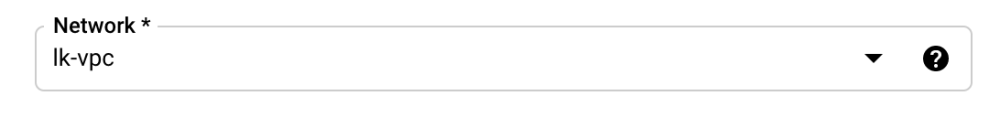
- Select Network as lk-vpc.
- Priority can be any value between 0 and 65535. Leave the default value of 1000. For other rules, you can use 1100, 1200, etc. This will allow for other priority values to be injected if additional rules are needed in the future.

- Select “Ingress” for “Direction of traffic” and “Allow” for “Action on match”. With these selections incoming traffic matched with patterns specified in the following steps are “Allowed”.

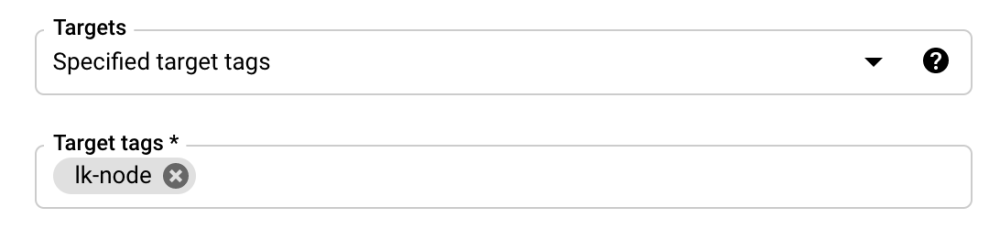
- Select Targets (destination of the traffic). Make sure to select the lk-node tag that is assigned to the VM you created.
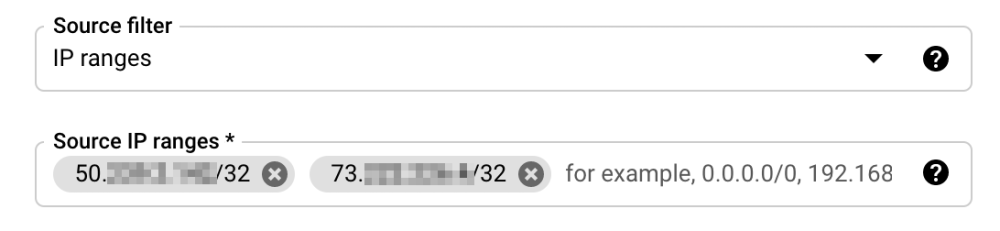
- Select source (WAN IP address(es) of your work location).
- Finally, select the protocol to allow. Confirm all values you have entered and create a rule.
- Now a rule is defined. Use the same steps to create other rules.


Post your comment on this topic.